如果你也在 怎样代写理论计算机theoretical computer science这个学科遇到相关的难题,请随时右上角联系我们的24/7代写客服。
理论计算机科学在精神上是数学的和抽象的,但它的动机来自于实际和日常的计算。它的目的是理解计算的本质,并作为这种理解的结果,提供更有效的方法论。
statistics-lab™ 为您的留学生涯保驾护航 在代写理论计算机theoretical computer science方面已经树立了自己的口碑, 保证靠谱, 高质且原创的统计Statistics代写服务。我们的专家在代写理论计算机theoretical computer science代写方面经验极为丰富,各种代写理论计算机theoretical computer science相关的作业也就用不着说。
我们提供的理论计算机theoretical computer science及其相关学科的代写,服务范围广, 其中包括但不限于:
- Statistical Inference 统计推断
- Statistical Computing 统计计算
- Advanced Probability Theory 高等概率论
- Advanced Mathematical Statistics 高等数理统计学
- (Generalized) Linear Models 广义线性模型
- Statistical Machine Learning 统计机器学习
- Longitudinal Data Analysis 纵向数据分析
- Foundations of Data Science 数据科学基础
数学代写|理论计算机代写theoretical computer science代考|Methodology
Figure 2 illustrates the overall scheme of our methodology. There are three main modules Trace Generator, Language Learner, and Classifier. The trace generator module converts the packet traces of each application into a word list by first splitting the traces by using the timing parameters and then applying the Map function to identified network units. Then, the k-TSS network language of the application is learned from its words by the Language Learner module. By applying this process for all applications, a database of k-TSS languages is obtained. To classify traffic of a system, first, the Trace Generator module extracts its sessions and their network units using the timing parameters. Then, it converts the sessions to the symbolic words to prepare the inputs of the Language Learner module. Finally, the Classifier module compares the learned language of each session of the given traffic against the languages of the database to label them. We describe each module in detail in the following.
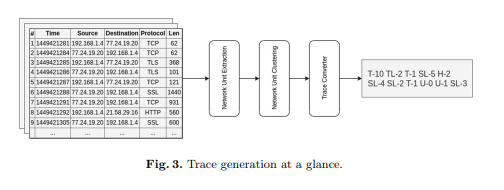
数学代写|理论计算机代写theoretical computer science代考|Trace Generator
The goal of the Trace Generator module is to transform the packet traces of each application into traces of smaller units, while preserving the relation among these units, as the letters of a language. To do so, at first, packet traces are split into smaller units, named network unit, by using the three timing parameters, introduced in Sect. 3. Then, these units are categorized based on their higherlayer protocol, and each category is clustered separately and named upon it. Consequently, the names of clusters constitute the Network Alphabet. Finally, the network alphabets are put in together to form our traces. Therefore, the input of this subproblem is $\Pi$ containing $m$ application traces and the timing parameters st, $f d$, and it, while the output is a set of word list $S=\left{W_{1}, W_{2}, \ldots, W_{m}\right}$, where $W_{i}$ is a list including the generated words of language $A p p_{i}$.
Network Unit Extraction. Network Units are extracted during three steps. At first, network traces are split into sessions based on the session threshold. Then, flow-sessions are extracted based on the inactive timeort. After that, flowsessions are divided into smaller units according to the flow duration constraint. Figure 1 shows the result of applying this module on a given trace to produce sessions, flow-sessions, and network units.
Network Unit Clustering. For naming network units, there is a need to group the similar ones and name them upon it. As there is no information on the number of units or their labels, an unsupervised machine learning algorithm named Kmeans $+t$ is used for clustering these units. The only information available for each flow are those stored in the frame header of its packets. Therefore, the clustering algorithm could benefit from the knowledge of the unit higher-layer protocol. Consequently, flows having the same protocol are at worst clustered together and named upon their protocol. The packets of each flow can be further clustered in terms of multiple statistical features listed in Table 1. Two groups of features are used for clustering network unit, the first group consists of features number one to six, and the second group includes features number three to nine. Regarding these two groups, the statistical features group (stats) is another configuration of this problem.
Moreover, it is required to set the number of clusters before performing the Kmeanst+ algorithm. To do so, the number of clusters is automatically determined with the help of the elbow [17] method in our approach.
Our defined Map function returns a concatenation of the symbol abbreviating packet protocol name and a natural number indicating its cluster number (to distinguish network units). For example, TL-5 corresponds to a packet sequence belonging to cluster 5 of the TLS protocol.
数学代写|理论计算机代写theoretical computer science代考|Language Learner
After preparation tasks, we obtain the modified word list $W^{\prime}=$ $\left[w_{1}^{\prime}, w_{2}^{\prime}, \ldots, w_{n}^{\prime}\right]$. Now, we learn a list of k-TSS languages for each $w^{\prime} \in$ $W^{\prime}$ as $\mathcal{L}\left(w^{\prime}\right)$ by a k-size frame scanner. For instance, for the given $w^{\prime}=$ SL-4 SL-2 T-10 TL-2 T-1 U-2, $\mathcal{L}\left(w^{\prime}\right)$ is obtained by k-TSS vector $Z\left(w^{\prime}\right)$ as $\langle\Sigma={\mathrm{SL}-2, \mathrm{TL}-2, \mathrm{~T}-1, \mathrm{U}-2, \mathrm{SL}-4, \mathrm{~T}-10}, I={\mathrm{SL}-4 \mathrm{SL}-2,}, F=$, ${\mathrm{T}-1 \mathrm{U}-2}, T={\mathrm{SL}-4 \mathrm{SL}-2 \mathrm{~T}-10, \mathrm{SL}-2 \mathrm{~T}-10 \mathrm{TL}-2, \mathrm{~T}-10 \mathrm{TL}-2 \mathrm{~T}-1, \mathrm{TL}-2$ T-1 U-2} .
To specify each word’s class, we observe its segments instead of exploring the whole word to be more noise tolerable. To this aim, we reduce the classification problem to find the similarity between the generated k-TTS languages of the trace and the ones in the database. For each k-TSS language in the database, we calculate its proximity with $\mathcal{L}\left(w^{\prime}\right)$ by a distance function defined as:
Definition 6 (Distance Function). Distance function $D$ measures the proximity metric between two k-TSS languages. Let $Z=\langle\Sigma, I, F, T\rangle$ be the $k$-test vector of $\mathcal{L}\left(w^{\prime}\right)$ and $Z_{i}=\left\langle\Sigma_{i}, I_{i}, F_{i}, T_{i}\right\rangle$ be the k-test vector of $\mathcal{L}\left(A p p_{i}\right)$. Then, $D\left(\mathcal{L}\left(w^{\prime}\right), \mathcal{L}\left(A p p_{i}\right)\right)$ is computed by five auciliary variables, measuring the sets diffenence fraction: $\triangle T, \Delta T_{i}, \Delta \Sigma, \triangle I$ and $\triangle F$ (defined in Eq. 1).
$\Delta T=\frac{T-T_{i}}{T}, \Delta T_{i}=\frac{T_{i}-T}{T_{i}}, \Delta \Sigma=\frac{\Sigma-\Sigma_{i}}{\Sigma}, \Delta I=\frac{I-I_{i}}{I}, \Delta F=\frac{F-F_{i}}{F} .$
$D\left(\mathcal{L}\left(w^{\prime}\right), \mathcal{L}\left(A p p_{i}\right)\right)=\overline{\Delta^{\prime} T} \overline{\triangle^{\prime} T_{i}} \overline{\Delta^{\prime} \Sigma} \overline{\triangle^{\prime} I} \overline{\triangle^{\prime} F}$
We assume a priority among these delta metrics as $\triangle T, \Delta T_{i}, \triangle \Sigma, \triangle I$ and $\triangle F$. Since $T$ carries more information of words than $I$ and $F$, we assign the highest priority to $\triangle T$. Also, we give $\triangle T$ higher priority than $\triangle T_{i}$, as $T$ is generated from a test trace in contrast to $T_{i}$ which is generated from a number of traces of an application. We specify the next priority to $\triangle \Sigma$ to take into account the alphabet sets differences. We assign the next priorities to $\triangle I$ and then $\triangle F$, respectively, because the trimming operation of the preparation phase may impact on the end of the words while their initials are not modified. Finally, we convert the value of delta metrics from a float number in the range $[0,1]$ to an integer number in the range $[0,99]$, renaming them by a prime sign, for example, $\triangle^{\prime} T$. By this priority, the distance function is defined as given by Eq. 2 .
A word $w$ is categorized in class $j$ if the k-TSS language of $w$ has the minimum distance with the k-TSS language of $A p p_{j}$ among all the applications:
$$
\operatorname{Class}\left(w^{\prime}\right)=j \Longleftrightarrow \text { if } D\left(\mathcal{L}\left(w^{\prime}\right), \mathcal{L}\left(A p p_{j}\right)\right)=\operatorname{argmin}{\forall A p p{i} \in|\mathcal{A}|}\left(D\left(\mathcal{L}\left(w^{\prime}\right), \mathcal{L}\left(A p p_{i}\right)\right)\right)
$$
Considering the running example $\left(\mathcal{L}\left(A p p_{i}\right)\right.$ in Sect. $4.2$ and $\left.\mathcal{L}\left(w^{\prime}\right)\right)$, the defined delta metrics are obtained as $\triangle T=0.75\left(\triangle^{\prime} T=74\right), \Delta T_{i}=0.85$ $\left(\triangle^{\prime} T_{i}=84\right), \triangle \Sigma=0.16\left(\triangle^{\prime} \Sigma=16\right), \triangle I=0\left(\triangle^{\prime} I=0\right)$, and $\triangle F=1\left(\triangle^{\prime} F=\right.$ $99)$ and finally, the distance is computed as $D\left(\mathcal{L}\left(w^{\prime}\right), \mathcal{L}\left(A p p_{i}\right)\right)=7484160099 .$
理论计算机代写
数学代写|理论计算机代写theoretical computer science代考|Methodology
图 2 说明了我们方法的总体方案。共有三个主要模块 Trace Generator、Language Learner 和 Classifier。跟踪生成器模块首先使用时序参数拆分跟踪,然后将映射函数应用于识别的网络单元,从而将每个应用程序的数据包跟踪转换为单词列表。然后,Language Learner 模块从其单词中学习应用程序的 k-TSS 网络语言。通过将此过程应用于所有应用程序,可以获得 k-TSS 语言的数据库。为了对系统的流量进行分类,首先,跟踪生成器模块使用时序参数提取其会话及其网络单元。然后,它将会话转换为符号词以准备语言学习器模块的输入。最后,分类器模块将给定流量的每个会话的学习语言与数据库的语言进行比较以标记它们。我们将在下面详细描述每个模块。
数学代写|理论计算机代写theoretical computer science代考|Trace Generator
Trace Generator 模块的目标是将每个应用程序的数据包跟踪转换为较小单元的跟踪,同时将这些单元之间的关系保留为语言的字母。为此,首先,通过使用第 3 节中介绍的三个时间参数,将数据包跟踪分成更小的单元,称为网络单元。3. 然后,这些单元根据它们的高层协议进行分类,每个类别被单独聚类并命名。因此,集群的名称构成了网络字母表。最后,将网络字母组合在一起形成我们的踪迹。因此,这个子问题的输入是圆周率包含米应用程序跟踪和时序参数 st,Fd, 而它, 而输出是一组单词列表S=\left{W_{1}, W_{2}, \ldots, W_{m}\right}S=\left{W_{1}, W_{2}, \ldots, W_{m}\right}, 在哪里在一世是一个列表,包括生成的语言单词一种pp一世.
网络单元提取。在三个步骤中提取网络单元。首先,网络跟踪根据会话阈值拆分为会话。然后,基于非活动时间排序提取流会话。之后,根据流持续时间约束将流会话划分为更小的单元。图 1 显示了在给定跟踪上应用此模块以生成会话、流会话和网络单元的结果。
网络单元聚类。对于命名网络单元,需要将相似的单元分组并在其上命名。由于没有关于单元数量或其标签的信息,一种名为 Kmeans 的无监督机器学习算法+吨用于对这些单元进行聚类。每个流唯一可用的信息是存储在其数据包的帧头中的信息。因此,聚类算法可以受益于单元高层协议的知识。因此,具有相同协议的流在最坏的情况下聚集在一起并根据它们的协议命名。每个流的数据包可以根据表1中列出的多个统计特征进一步聚类。两组特征用于聚类网络单元,第一组由1到6号特征组成,第二组包括3号特征到九点。关于这两组,统计特征组(stats)是这个问题的另一种配置。
此外,在执行 Kmeanst+ 算法之前需要设置簇的数量。为此,在我们的方法中,借助肘部 [17] 方法自动确定聚类的数量。
我们定义的 Map 函数返回一个连接的符号,缩写数据包协议名称和一个表示其簇号的自然数(以区分网络单元)。例如,TL-5 对应于属于 TLS 协议簇 5 的数据包序列。
数学代写|理论计算机代写theoretical computer science代考|Language Learner
在准备任务之后,我们得到修改后的词表在′= [在1′,在2′,…,在n′]. 现在,我们为每个学习一个 k-TSS 语言列表在′∈ 在′作为大号(在′)通过 k 尺寸帧扫描仪。例如,对于给定的在′=SL-4 SL-2 T-10 TL-2 T-1 U-2,大号(在′)由 k-TSS 向量获得从(在′)作为⟨Σ=小号大号−2,吨大号−2, 吨−1,在−2,小号大号−4, 吨−10,一世=小号大号−4小号大号−2,,F=, $ {\ mathrm {T} -1 \ mathrm {U} -2}, T = {\ mathrm {SL} -4 \ mathrm {SL} -2 \ mathrm ~ T} -10, \ mathrm {SL -2 \ mathrm {~ T} -10 \ mathrm {TL} -2, \ mathrm ~ T} -10 \ mathrm {TL} -2 \ mathrm ~ T} -1, \ mathrm {TL} -2 $ T-1 U -2。
为了指定每个单词的类别,我们观察它的片段而不是探索整个单词以便更能容忍噪声。为此,我们减少了分类问题,以找到生成的 k-TTS 语言与数据库中的语言之间的相似性。对于数据库中的每种 k-TSS 语言,我们计算其与大号(在′)通过定义为的距离函数:
定义 6(距离函数)。距离函数D测量两种 k-TSS 语言之间的接近度度量。让从=⟨Σ,一世,F,吨⟩成为ķ-测试向量大号(在′)和从一世=⟨Σ一世,一世一世,F一世,吨一世⟩是 k 检验向量大号(一种pp一世). 然后,D(大号(在′),大号(一种pp一世))由五个辅助变量计算,测量集合差异分数:△吨,Δ吨一世,ΔΣ,△一世和△F(在等式 1 中定义)。
Δ吨=吨−吨一世吨,Δ吨一世=吨一世−吨吨一世,ΔΣ=Σ−Σ一世Σ,Δ一世=一世−一世一世一世,ΔF=F−F一世F.
D(大号(在′),大号(一种pp一世))=Δ′吨¯△′吨一世¯Δ′Σ¯△′一世¯△′F¯
我们假设这些增量指标中的优先级为△吨,Δ吨一世,△Σ,△一世和△F. 自从吨携带比单词更多的信息一世和F,我们将最高优先级分配给△吨. 另外,我们给△吨优先级高于△吨一世, 作为吨是从测试轨迹生成的,而不是吨一世它是从应用程序的许多跟踪生成的。我们指定下一个优先级△Σ考虑到字母集的差异。我们将下一个优先级分配给△一世进而△F,分别是因为准备阶段的修剪操作可能会影响单词的结尾,而它们的首字母不会被修改。最后,我们将增量指标的值从范围内的浮点数转换为[0,1]范围内的整数[0,99],用一个主要符号重命名它们,例如,△′吨. 通过这个优先级,距离函数被定义为由等式给出。2.
一个字在被分类在类j如果 k-TSS 语言在与 k-TSS 语言的距离最小一种ppj在所有应用程序中:
班级(在′)=j⟺ 如果 D(大号(在′),大号(一种ppj))=精氨酸∀一种pp一世∈|一种|(D(大号(在′),大号(一种pp一世)))
考虑运行示例(大号(一种pp一世)昆虫。4.2和大号(在′)), 定义的 delta 度量被获得为△吨=0.75(△′吨=74),Δ吨一世=0.85 (△′吨一世=84),△Σ=0.16(△′Σ=16),△一世=0(△′一世=0), 和△F=1(△′F= 99)最后,距离计算为D(大号(在′),大号(一种pp一世))=7484160099.
统计代写请认准statistics-lab™. statistics-lab™为您的留学生涯保驾护航。
金融工程代写
金融工程是使用数学技术来解决金融问题。金融工程使用计算机科学、统计学、经济学和应用数学领域的工具和知识来解决当前的金融问题,以及设计新的和创新的金融产品。
非参数统计代写
非参数统计指的是一种统计方法,其中不假设数据来自于由少数参数决定的规定模型;这种模型的例子包括正态分布模型和线性回归模型。
广义线性模型代考
广义线性模型(GLM)归属统计学领域,是一种应用灵活的线性回归模型。该模型允许因变量的偏差分布有除了正态分布之外的其它分布。
术语 广义线性模型(GLM)通常是指给定连续和/或分类预测因素的连续响应变量的常规线性回归模型。它包括多元线性回归,以及方差分析和方差分析(仅含固定效应)。
有限元方法代写
有限元方法(FEM)是一种流行的方法,用于数值解决工程和数学建模中出现的微分方程。典型的问题领域包括结构分析、传热、流体流动、质量运输和电磁势等传统领域。
有限元是一种通用的数值方法,用于解决两个或三个空间变量的偏微分方程(即一些边界值问题)。为了解决一个问题,有限元将一个大系统细分为更小、更简单的部分,称为有限元。这是通过在空间维度上的特定空间离散化来实现的,它是通过构建对象的网格来实现的:用于求解的数值域,它有有限数量的点。边界值问题的有限元方法表述最终导致一个代数方程组。该方法在域上对未知函数进行逼近。[1] 然后将模拟这些有限元的简单方程组合成一个更大的方程系统,以模拟整个问题。然后,有限元通过变化微积分使相关的误差函数最小化来逼近一个解决方案。
tatistics-lab作为专业的留学生服务机构,多年来已为美国、英国、加拿大、澳洲等留学热门地的学生提供专业的学术服务,包括但不限于Essay代写,Assignment代写,Dissertation代写,Report代写,小组作业代写,Proposal代写,Paper代写,Presentation代写,计算机作业代写,论文修改和润色,网课代做,exam代考等等。写作范围涵盖高中,本科,研究生等海外留学全阶段,辐射金融,经济学,会计学,审计学,管理学等全球99%专业科目。写作团队既有专业英语母语作者,也有海外名校硕博留学生,每位写作老师都拥有过硬的语言能力,专业的学科背景和学术写作经验。我们承诺100%原创,100%专业,100%准时,100%满意。
随机分析代写
随机微积分是数学的一个分支,对随机过程进行操作。它允许为随机过程的积分定义一个关于随机过程的一致的积分理论。这个领域是由日本数学家伊藤清在第二次世界大战期间创建并开始的。
时间序列分析代写
随机过程,是依赖于参数的一组随机变量的全体,参数通常是时间。 随机变量是随机现象的数量表现,其时间序列是一组按照时间发生先后顺序进行排列的数据点序列。通常一组时间序列的时间间隔为一恒定值(如1秒,5分钟,12小时,7天,1年),因此时间序列可以作为离散时间数据进行分析处理。研究时间序列数据的意义在于现实中,往往需要研究某个事物其随时间发展变化的规律。这就需要通过研究该事物过去发展的历史记录,以得到其自身发展的规律。
回归分析代写
多元回归分析渐进(Multiple Regression Analysis Asymptotics)属于计量经济学领域,主要是一种数学上的统计分析方法,可以分析复杂情况下各影响因素的数学关系,在自然科学、社会和经济学等多个领域内应用广泛。
MATLAB代写
MATLAB 是一种用于技术计算的高性能语言。它将计算、可视化和编程集成在一个易于使用的环境中,其中问题和解决方案以熟悉的数学符号表示。典型用途包括:数学和计算算法开发建模、仿真和原型制作数据分析、探索和可视化科学和工程图形应用程序开发,包括图形用户界面构建MATLAB 是一个交互式系统,其基本数据元素是一个不需要维度的数组。这使您可以解决许多技术计算问题,尤其是那些具有矩阵和向量公式的问题,而只需用 C 或 Fortran 等标量非交互式语言编写程序所需的时间的一小部分。MATLAB 名称代表矩阵实验室。MATLAB 最初的编写目的是提供对由 LINPACK 和 EISPACK 项目开发的矩阵软件的轻松访问,这两个项目共同代表了矩阵计算软件的最新技术。MATLAB 经过多年的发展,得到了许多用户的投入。在大学环境中,它是数学、工程和科学入门和高级课程的标准教学工具。在工业领域,MATLAB 是高效研究、开发和分析的首选工具。MATLAB 具有一系列称为工具箱的特定于应用程序的解决方案。对于大多数 MATLAB 用户来说非常重要,工具箱允许您学习和应用专业技术。工具箱是 MATLAB 函数(M 文件)的综合集合,可扩展 MATLAB 环境以解决特定类别的问题。可用工具箱的领域包括信号处理、控制系统、神经网络、模糊逻辑、小波、仿真等。
