如果你也在 怎样代写博弈论Game Theory这个学科遇到相关的难题,请随时右上角联系我们的24/7代写客服。
博弈论是对理性主体之间战略互动的数学模型的研究。它在社会科学的所有领域,以及逻辑学、系统科学和计算机科学中都有应用。最初,它针对的是两人的零和博弈,其中每个参与者的收益或损失都与其他参与者的收益或损失完全平衡。在21世纪,博弈论适用于广泛的行为关系;它现在是人类、动物以及计算机的逻辑决策科学的一个总称。
statistics-lab™ 为您的留学生涯保驾护航 在代写博弈论Game Theory方面已经树立了自己的口碑, 保证靠谱, 高质且原创的统计Statistics代写服务。我们的专家在代写博弈论Game Theory代写方面经验极为丰富,各种代写博弈论Game Theory相关的作业也就用不着说。
我们提供的博弈论Game Theory及其相关学科的代写,服务范围广, 其中包括但不限于:
- Statistical Inference 统计推断
- Statistical Computing 统计计算
- Advanced Probability Theory 高等概率论
- Advanced Mathematical Statistics 高等数理统计学
- (Generalized) Linear Models 广义线性模型
- Statistical Machine Learning 统计机器学习
- Longitudinal Data Analysis 纵向数据分析
- Foundations of Data Science 数据科学基础
经济代写|博弈论代写Game Theory代考|Stackelberg Security Games
A special class of Stackelberg games is the Stackelberg security game (SSG). The SSG model has wide applications in security-related domains. It has led to several application tools successfully deployed in the field, including ARMOR for setting up checkpoints and scheduling canine patrols at the Los Angeles International Airport, PROTECT for protecting ports of New York and Boston (Tambe 2011), and PAWS for protecting wildlife from poaching (Fang et al. 2016).
An SSG (Kiekintveld et al. 2009; Paruchuri et al. 2008) is a two-player game between a defender and an attacker. The defender must protect a set of $T$ targets from the attacker. The defender tries to prevent attacks using $M$ defender resources. In the simplest case, each defender resource (which corresponds to a patroller, a checkpoint, a canine team, or a ranger in security-related domains) can be allocated to protect one target and $M<T$. Thus, a pure strategy for the defender is an assignment of the $M$ resources to $M$ targets and a pure strategy for the adversary is a target $k \in{1 \ldots T}$ to be attacked. In a slightly more complex setting, each defender resource can be assigned to a patrol schedule, which covers a subset of targets, and it is impossible to cover all the targets with limited resources. Denote the jth defender pure strategy as $B_{j}$, an assignment of all the security resources. $B_{j}$ is represented as a column vector $B_{j}=\left\langle B_{j k}\right\rangle^{T}$, where $B_{j k} \in{0,1}$ indicates whether target $k$ is covered by $B_{j}$. For example, in a game with four targets and two resources, each of which can cover one target, $B_{j}=\langle 1,1,0,0\rangle$ represents the pure strategy of assigning one resource to target 1 and another to target 2. Each target $k \in{1 \ldots T}$ is assigned a set of payoffs $\left{P_{k}^{a}, R_{k}^{a}, P_{k}^{d}, R_{k}^{d}\right}:$ If an attacker attacks target $k$ and it is protected by a defender resource, the attacker gets utility $P_{k}^{a}$ and the defender gets utility $R_{k}^{d}$. If target $k$ is not protected, the attacker gets utility $R_{k}^{a}$ and the defender gets utility $P_{k}^{d}$. In order to be a valid security game, it must hold that $R_{k}^{a}>P_{k}^{d}$ and $R_{k}^{d}>P_{k}^{d}$, i.e. when the attacked target is covered, the defender gets a utility higher than that when it is not covered, and the opposite holds for the attacker. The defender is the leader and commits to a strategy first. The attacker can observe the defender’s strategy before selecting their strategy. This assumption reflects what happens in the real world in many cases. For example, in the airport security domain, the airport security team sends canine teams to protect the terminals every day. A dedicated attacker may be able to conduct surveillance to learn the defender’s strategy.
经济代写|博弈论代写Game Theory代考|Applications in Cybersecurity
Several works have used the Stackelberg game model to formulate problems in cybersecurity. Schlenker et al. (2018) and Thakoor et al. (2019) model the cyber deception problem as a Stackelberg game between the defender and the attacker. Similar to SSGs, the defender is protecting a set of targets from the attacker. In contrast to SSGs where the defender allocates resources to stop any potential attack on a subset of targets, in this work, the defender can choose to set up honeypots or provide a camouflage of existing machines in a network. By such deception techniques, the defender can make the honeypots appear to be important, or value targets appear unimportant. Thus, she can induce the attacker to attack a unimportant to the defender. Cranford et al. (2018) focuses on human behavior in cyber deception games. Schlenker et al. (2017) proposes a Stackelberg game model for the problem of allocating limited human limited human resources to investigate cybersecurity alerts. Stackelberg game models have also been used to model defense in cyber-physical systems (Wang et al. 2018; Yuan et al. 2016; Zhu and Martinez 2011). Li and Vorobeychik (2014, 2015) considers the detection and filtering of spam and phishing emails and formulate the problem as a Stackelberg game where an intelligent attacker will try to adapt to the defense strategy.
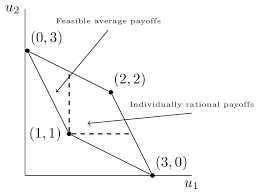
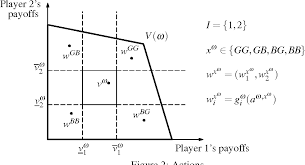
经济代写|博弈论代写Game Theory代考|Repeated Games
A repeated game is an EFG consisting of repetitions of a stage game. The stage game can be an NFG. For example, the repeated PD game is a game where the players repeatedly play the stage game of a PD game for multiple rounds. Also, we often see people playing the RPS game for three or five consecutive rounds in practice. A finitely repeated game has a finite number of rounds, and a player’s final payoff is the sum of their payoffs in each round. Infinitely repeated games last forever; there can be a discount factor $\delta \in(0,1)$ for future rounds when computing the final payoff.
The repetition of the stage game enables a much larger strategy space for the players comparing with the strategy space of the stage game. A player’s action in a round can be based on the players’ actions in the previous rounds. For example, in the repeated PD game, a player can use a Tit-for-Tat strategy, meaning that the player always chooses the same action as the one taken by the other player in the previous round of the game except for the first round where the player chooses Cooperate. In other words, if her opponent chose Cooperate in the last round, she will reward the other player’s kindness by choosing Cooperate in this round. Otherwise, she will penalize the other player by choosing Defect. A player can also choose a grim trigger strategy: she chooses Cooperate in the first round and continues to choose Cooperate if the other player never chooses Defect, but penalizes the other player by always choosing Defect for the rest of the game right after the other player chooses Defect for the first time.
In fact, both players playing the grim trigger strategy is an NE in an infinitely repeated PD game, as a player who deviates from it will get a utility of 0 in the round he deviates but at most $-2$ for each round in the rest of the game as the other player will always choose Defect. Both players choosing Tit-for-Tat is also an NE with a large enough $\delta$. If the player deviates by choosing Defect for $k-1$ consecutive rounds starting from round $t$ and then chooses Cooperate again, he can get at most a total utility of $0+\delta \times(-2)+\delta^{2} \times(-2)+\cdots+\delta^{k-1} \times(-2)+\delta^{k} \times(-3)$ for round $t$ to $t+k$. In comparison, not deviating leads to a total utility of $(-1)+\delta \cdot(-1)+\cdots+\delta^{k} \cdot(-1)$ during this period.
博弈论代考
经济代写|博弈论代写Game Theory代考|Stackelberg Security Games
一种特殊的 Stackelberg 游戏是 Stackelberg 安全游戏 (SSG)。SSG 模型在安全相关领域有着广泛的应用。它已导致在该领域成功部署了多种应用工具,包括用于在洛杉矶国际机场设置检查站和安排犬类巡逻的 ARMOR、用于保护纽约和波士顿港口的 PROTECT(Tambe 2011)以及用于保护野生动物免受伤害的 PAWS偷猎(Fang et al. 2016)。
SSG (Kiekintveld et al. 2009; Paruchuri et al. 2008) 是防守方和进攻方之间的两人游戏。防守方必须保护一组吨攻击者的目标。防御者试图阻止攻击使用米后卫资源。在最简单的情况下,每个防御者资源(对应于巡逻员、检查站、警犬队或安全相关域中的游侠)可以被分配来保护一个目标和米<吨. 因此,防御者的纯策略是米资源米目标和对对手的纯粹策略是目标ķ∈1…吨被攻击。在稍微复杂的设置中,每个防御者资源都可以分配到一个巡逻计划,该计划涵盖目标的子集,并且不可能在资源有限的情况下覆盖所有目标。将第 j 个防御者纯策略表示为乙j,所有安全资源的分配。乙j表示为列向量乙j=⟨乙jķ⟩吨, 在哪里乙jķ∈0,1表示目标是否ķ被覆盖乙j. 例如,在一个有四个目标和两个资源的游戏中,每个资源可以覆盖一个目标,乙j=⟨1,1,0,0⟩表示将一种资源分配给目标 1 并将另一种资源分配给目标 2 的纯策略。每个目标ķ∈1…吨分配了一组收益\left{P_{k}^{a}, R_{k}^{a}, P_{k}^{d}, R_{k}^{d}\right}:\left{P_{k}^{a}, R_{k}^{a}, P_{k}^{d}, R_{k}^{d}\right}:如果攻击者攻击目标ķ它受到防御者资源的保护,攻击者获得效用磷ķ一个防御者得到效用Rķd. 如果目标ķ不受保护,攻击者获得实用程序Rķ一个防御者得到效用磷ķd. 为了成为一个有效的安全游戏,它必须持有Rķ一个>磷ķd和Rķd>磷ķd,即当被攻击的目标被覆盖时,防御者获得的效用高于没有被覆盖时的效用,而攻击者则相反。防御者是领导者,首先致力于战略。攻击者可以在选择他们的策略之前观察防御者的策略。这一假设反映了现实世界中许多情况下发生的情况。例如,在机场安检领域,机场安检队每天都会派出警犬队来保护航站楼。专门的攻击者可能能够进行监视以了解防御者的策略。
经济代写|博弈论代写Game Theory代考|Applications in Cybersecurity
有几部作品使用了 Stackelberg 博弈模型来阐述网络安全中的问题。施伦克等人。(2018 年)和 Thakoor 等人。(2019)将网络欺骗问题建模为防御者和攻击者之间的 Stackelberg 博弈。与 SSG 类似,防御者正在保护一组目标免受攻击者的攻击。与防御者分配资源以阻止对目标子集的任何潜在攻击的 SSG 相比,在这项工作中,防御者可以选择设置蜜罐或提供网络中现有机器的伪装。通过这种欺骗技术,防御者可以使蜜罐显得很重要,或者价值目标显得不重要。因此,她可以诱导攻击者攻击一个对防御者来说不重要的东西。克兰福德等人。(2018)专注于网络欺骗游戏中的人类行为。施伦克等人。(2017) 提出了一个 Stackelberg 博弈模型,用于解决分配有限人力资源来调查网络安全警报的问题。Stackelberg 博弈模型也被用于模拟网络物理系统中的防御(Wang et al. 2018; Yuan et al. 2016; Zhu and Martinez 2011)。Li and Vorobeychik (2014, 2015) 考虑了垃圾邮件和网络钓鱼电子邮件的检测和过滤,并将问题表述为一个 Stackelberg 博弈,其中智能攻击者将尝试适应防御策略。
经济代写|博弈论代写Game Theory代考|Repeated Games
重复游戏是由阶段游戏的重复组成的 EFG。舞台游戏可以是NFG。例如,重复PD游戏是玩家反复玩PD游戏的阶段游戏多轮的游戏。此外,我们经常看到人们在练习中连续玩三五轮 RPS 游戏。有限重复游戏的轮数有限,玩家的最终收益是他们在每一轮中收益的总和。无限重复的游戏永远持续;可能有折扣因素d∈(0,1)计算最终收益时的未来轮次。
与舞台游戏的策略空间相比,舞台游戏的重复为玩家提供了更大的策略空间。玩家在一轮中的动作可以基于玩家在前几轮中的动作。例如,在重复的 PD 游戏中,玩家可以使用以牙还牙的策略,这意味着玩家总是选择与前一轮游戏中其他玩家所采取的行动相同的动作,但第一轮除外玩家选择合作的地方。换句话说,如果她的对手在上一轮选择了合作,她将在这一轮选择合作来奖励对方玩家的好意。否则,她将通过选择缺陷来惩罚其他玩家。玩家还可以选择严峻的触发策略:
事实上,在无限重复的 PD 博弈中,玩严峻触发策略的两个玩家都是 NE,因为偏离它的玩家在他偏离的回合中的效用为 0,但最多−2在游戏剩余的每一轮中,其他玩家总是会选择缺陷。选择以牙还牙的两个玩家也是一个足够大的NEd. 如果玩家因选择缺陷而偏离ķ−1从回合开始的连续回合吨然后再次选择合作,他最多可以得到总效用0+d×(−2)+d2×(−2)+⋯+dķ−1×(−2)+dķ×(−3)圆形吨至吨+ķ. 相比之下,不偏离会导致总效用(−1)+d⋅(−1)+⋯+dķ⋅(−1)在这段时期。
统计代写请认准statistics-lab™. statistics-lab™为您的留学生涯保驾护航。
金融工程代写
金融工程是使用数学技术来解决金融问题。金融工程使用计算机科学、统计学、经济学和应用数学领域的工具和知识来解决当前的金融问题,以及设计新的和创新的金融产品。
非参数统计代写
非参数统计指的是一种统计方法,其中不假设数据来自于由少数参数决定的规定模型;这种模型的例子包括正态分布模型和线性回归模型。
广义线性模型代考
广义线性模型(GLM)归属统计学领域,是一种应用灵活的线性回归模型。该模型允许因变量的偏差分布有除了正态分布之外的其它分布。
术语 广义线性模型(GLM)通常是指给定连续和/或分类预测因素的连续响应变量的常规线性回归模型。它包括多元线性回归,以及方差分析和方差分析(仅含固定效应)。
有限元方法代写
有限元方法(FEM)是一种流行的方法,用于数值解决工程和数学建模中出现的微分方程。典型的问题领域包括结构分析、传热、流体流动、质量运输和电磁势等传统领域。
有限元是一种通用的数值方法,用于解决两个或三个空间变量的偏微分方程(即一些边界值问题)。为了解决一个问题,有限元将一个大系统细分为更小、更简单的部分,称为有限元。这是通过在空间维度上的特定空间离散化来实现的,它是通过构建对象的网格来实现的:用于求解的数值域,它有有限数量的点。边界值问题的有限元方法表述最终导致一个代数方程组。该方法在域上对未知函数进行逼近。[1] 然后将模拟这些有限元的简单方程组合成一个更大的方程系统,以模拟整个问题。然后,有限元通过变化微积分使相关的误差函数最小化来逼近一个解决方案。
tatistics-lab作为专业的留学生服务机构,多年来已为美国、英国、加拿大、澳洲等留学热门地的学生提供专业的学术服务,包括但不限于Essay代写,Assignment代写,Dissertation代写,Report代写,小组作业代写,Proposal代写,Paper代写,Presentation代写,计算机作业代写,论文修改和润色,网课代做,exam代考等等。写作范围涵盖高中,本科,研究生等海外留学全阶段,辐射金融,经济学,会计学,审计学,管理学等全球99%专业科目。写作团队既有专业英语母语作者,也有海外名校硕博留学生,每位写作老师都拥有过硬的语言能力,专业的学科背景和学术写作经验。我们承诺100%原创,100%专业,100%准时,100%满意。
随机分析代写
随机微积分是数学的一个分支,对随机过程进行操作。它允许为随机过程的积分定义一个关于随机过程的一致的积分理论。这个领域是由日本数学家伊藤清在第二次世界大战期间创建并开始的。
时间序列分析代写
随机过程,是依赖于参数的一组随机变量的全体,参数通常是时间。 随机变量是随机现象的数量表现,其时间序列是一组按照时间发生先后顺序进行排列的数据点序列。通常一组时间序列的时间间隔为一恒定值(如1秒,5分钟,12小时,7天,1年),因此时间序列可以作为离散时间数据进行分析处理。研究时间序列数据的意义在于现实中,往往需要研究某个事物其随时间发展变化的规律。这就需要通过研究该事物过去发展的历史记录,以得到其自身发展的规律。
回归分析代写
多元回归分析渐进(Multiple Regression Analysis Asymptotics)属于计量经济学领域,主要是一种数学上的统计分析方法,可以分析复杂情况下各影响因素的数学关系,在自然科学、社会和经济学等多个领域内应用广泛。
MATLAB代写
MATLAB 是一种用于技术计算的高性能语言。它将计算、可视化和编程集成在一个易于使用的环境中,其中问题和解决方案以熟悉的数学符号表示。典型用途包括:数学和计算算法开发建模、仿真和原型制作数据分析、探索和可视化科学和工程图形应用程序开发,包括图形用户界面构建MATLAB 是一个交互式系统,其基本数据元素是一个不需要维度的数组。这使您可以解决许多技术计算问题,尤其是那些具有矩阵和向量公式的问题,而只需用 C 或 Fortran 等标量非交互式语言编写程序所需的时间的一小部分。MATLAB 名称代表矩阵实验室。MATLAB 最初的编写目的是提供对由 LINPACK 和 EISPACK 项目开发的矩阵软件的轻松访问,这两个项目共同代表了矩阵计算软件的最新技术。MATLAB 经过多年的发展,得到了许多用户的投入。在大学环境中,它是数学、工程和科学入门和高级课程的标准教学工具。在工业领域,MATLAB 是高效研究、开发和分析的首选工具。MATLAB 具有一系列称为工具箱的特定于应用程序的解决方案。对于大多数 MATLAB 用户来说非常重要,工具箱允许您学习和应用专业技术。工具箱是 MATLAB 函数(M 文件)的综合集合,可扩展 MATLAB 环境以解决特定类别的问题。可用工具箱的领域包括信号处理、控制系统、神经网络、模糊逻辑、小波、仿真等。
