如果你也在 怎样代写编码理论Coding Theory这个学科遇到相关的难题,请随时右上角联系我们的24/7代写客服。
编码理论是研究编码的属性和它们各自对特定应用的适用性。编码被用于数据压缩、密码学、错误检测和纠正、数据传输和数据存储。各种科学学科,如信息论、电气工程、数学、语言学和计算机科学,都对编码进行了研究,目的是设计高效和可靠的数据传输方法。这通常涉及消除冗余和纠正或检测传输数据中的错误。
statistics-lab™ 为您的留学生涯保驾护航 在代写编码理论Coding Theory方面已经树立了自己的口碑, 保证靠谱, 高质且原创的统计Statistics代写服务。我们的专家在代写编码理论Coding Theory代写方面经验极为丰富,各种代写编码理论Coding Theory相关的作业也就用不着说。
我们提供的编码理论Coding Theory及其相关学科的代写,服务范围广, 其中包括但不限于:
- Statistical Inference 统计推断
- Statistical Computing 统计计算
- Advanced Probability Theory 高等概率论
- Advanced Mathematical Statistics 高等数理统计学
- (Generalized) Linear Models 广义线性模型
- Statistical Machine Learning 统计机器学习
- Longitudinal Data Analysis 纵向数据分析
- Foundations of Data Science 数据科学基础
数学代写|编码理论作业代写Coding Theory代考|Bounds for Linear Block Codes
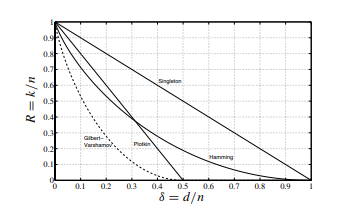
The code rate $R=k / n$ and the minimum Hamming distance $d$ are important parameters of a linear block code $\mathrm{B}(n, k, d)$. It is therefore useful to know whether a linear block code theoretically exists for a given combination of $R$ and $d$. In particular, for a given minimum Hamming distance $d$ we will consider a linear block code to be better than another linear block code with the same minimum Hamming distance $d$ if it has a higher code rate $R$. There exist several theoretical bounds which we will briefly discuss in the following (Berlekamp, 1984; Bossert, 1999; Ling and Xing, 2004; van Lint, 1999) (see also Figure 2.22). Block codes that fulfil a theoretical bound with equality are called optimal codes.
Singleton Bound
The simplest bound is the so-called Singleton bound. For a linear block code $\mathrm{B}(n, k, d)$ it is given by
$$
k \leq n-d+1 .
$$
A linear block code that fulfils the Singleton bound with equality according to $k=n-d+$ 1 is called MDS (maximum distance separable). Important representatives of MDS codes are Reed-Solomon codes which are used, for example, in the channel coding scheme within the audio compact disc (see also Section 2.3.7).
Sphere Packing Bound
The so-called sphere packing bound or Hamming bound can be derived for a linear $e_{\text {cor }}=$ $\lfloor(d-1) / 2\rfloor$-error correcting $q$-nary block code $\mathrm{B}(n, k, d)$ by considering the correction balls within the code space $\mathbb{F}{q}^{n}$. Each correction ball encompasses a total of $$ \sum{i=0}^{e_{\mathrm{cor}}}\left(\begin{array}{l}
n \
i
\end{array}\right)(q-1)^{i}
$$
vectors in the code space $F_{q}^{n}$. Since there is exactly one correction ball for each code word, we have $M=q^{k}$ correction balls. The total number of vectors within any correction ball of radius $e_{\text {cor }}$ is then given by
$$
q^{k} \sum_{i=0}^{e_{\text {cor }}}\left(\begin{array}{l}
n \
i
\end{array}\right)(q-1)^{i}
$$
Because this number must be smaller than or equal to the maximum number $\left|\mathbb{F}{q}^{n}\right|=q^{n}$ of vectors in the finite vector space $\mathbb{F}{q}^{n}$, the sphere packing bound
$$
q^{k} \sum_{i=0}^{e_{\operatorname{cor}}}\left(\begin{array}{l}
n \
i
\end{array}\right)(q-1)^{i} \leq q^{n}
$$
数学代写|编码理论作业代写Coding Theory代考|Plotkin’s (u|v) Code Construction
In contrast to the aforementioned code constructions, the (u|v) code construction originally proposed by Plotkin takes two linear block codes $\mathrm{B}\left(n_{1}, k_{1}, d_{1}\right)$ and $\mathrm{B}\left(n_{2}, k_{2}, d_{2}\right)$ with code word lengths $n_{1}$ and $n_{2}$, information word lengths $k_{1}$ and $k_{2}$ and minimum Hamming distances $d_{1}$ and $d_{2}$. For simplification, we fill the code words of the block code with smaller code word length by an appropriate number of zeros. This step is called zero padding. Let $\mathbf{u}$ and $\mathbf{v}$ be two arbitrary code words thus obtained from the linear block codes $\mathrm{B}\left(n_{1}, k_{1}, d_{1}\right)$ and $\mathrm{B}\left(n_{2}, k_{2}, d_{2}\right)$ respectively. ${ }^{12}$ Then we have
$$
\mathbf{u}= \begin{cases}\left(\mathbf{b}{1} \mid 0, \ldots, 0\right), & n{1}<n_{2} \ \mathbf{b}{1}, & n{1} \geq n_{2}\end{cases}
$$
and
$$
\mathbf{v}= \begin{cases}\mathbf{b}{2}, & n{1}<n_{2} \ \left(\mathbf{b}{2} \mid 0, \ldots, 0\right), & n{1} \geq n_{2}\end{cases}
$$
with the arbitrarily chosen code words $\mathbf{b}{1} \in \mathbb{B}\left(n{1}, k_{1}, d_{1}\right)$ and $\mathbf{b}{2} \in \mathbb{B}\left(n{2}, k_{2}, d_{2}\right)$. We now identify the code words $\mathbf{u}$ and $\mathbf{v}$ with the original codes $\mathrm{B}\left(n_{1}, k_{1}, d_{1}\right)$ and $\mathrm{B}\left(n_{2}, k_{2}, d_{2}\right)$, i.e. we write $\mathbf{u} \in \mathbb{B}\left(n_{1}, k_{1}, d_{1}\right)$ and $\mathbf{v} \in \mathbb{B}\left(n_{2}, k_{2}, d_{2}\right)$. The code resulting from Plotkin’s (u|v) code construction is then given by
$$
\mathbb{B}^{\prime}\left(n^{\prime}, k^{\prime}, d^{\prime}\right)=\left{(\mathbf{u} \mid \mathbf{u}+\mathbf{v}): \mathbf{u} \in \mathbb{B}\left(n_{1}, k_{1}, d_{1}\right) \wedge \mathbf{v} \in \mathbb{B}\left(n_{2}, k_{2}, d_{2}\right)\right}
$$
This code construction creates all vectors of the form $(\mathbf{u} \mid \mathbf{u}+\mathbf{v})$ by concatenating all possible vectors $\mathbf{u}$ and $\mathbf{u}+\mathbf{v}$ with $\mathbf{u} \in \mathbb{B}\left(n_{1}, k_{1}, d_{1}\right)$ and $\mathbf{v} \in \mathbb{B}\left(n_{2}, k_{2}, d_{2}\right)$. The resulting code is characterised by the following code parameters
$$
\begin{aligned}
&n^{\prime}=2 \max \left{n_{1}, n_{2}\right} \
&k^{\prime}=k_{1}+k_{2}, \
&d^{\prime}=\min \left{2 d_{1}, d_{2}\right}
\end{aligned}
$$
数学代写|编码理论作业代写Coding Theory代考|Examples of Linear Block Codes
In this section we will present some important linear block codes. In particular, we will consider the already introduced repetition codes, parity-check codes and Hamming codes. Furthermore, simplex codes and Reed-Muller codes and their relationships are discussed (Berlekamp, 1984; Bossert, 1999; Lin and Costello, 2004; Ling and Xing, 2004).
We have already introduced the binary triple repetition code in Section $1.3$ as a simple introductory example of linear block codes. In this particular code the binary information symbol 0 or 1 is transmitted with the binary code word 000 or 111 respectively. In general, a repetition code over the alphabet $\mathrm{F}{q}$ assigns to the $q$-nary information symbol $u{0}$ the $n$-dimensional code word $\mathbf{b}=\left(u_{0}, u_{0}, \ldots, u_{0}\right)$. Trivially, this block code is linear. The minimum Hamming distance is
$$
d=n .
$$
Therefore, the repetition code in Figure $2.27$ is a linear block code $\mathrm{B}(n, 1, n)$ that is able to detect $e_{\text {det }}=d-1=n-1$ errors or to correct $e_{\text {cor }}=\lfloor(d-1) / 2\rfloor=\lfloor(n-1) / 2\rfloor$ errors. The code rate is
$$
R=\frac{1}{n} .
$$
For the purpose of error correction, the minimum distance decoding can be implemented by a majority decoding scheme. The decoder emits the information symbol $\hat{u}_{0}$ which appears most often in the received word.
The weight distribution of a repetition code is simply given by
$$
W(x)=1+(q-1) x^{n}
$$
Although this repetition code is characterised by a low code rate $R$, it is used in some communication standards owing to its simplicity. For example, in the short-range wireless communication system Bluetooth ${ }^{\mathrm{TM}}$ a triple repetition code is used as part of the coding scheme of the packet header of a transmitted baseband packet (Bluetooth, 2004).
编码理论代写
数学代写|编码理论作业代写Coding Theory代考|Bounds for Linear Block Codes
码率R=ķ/n和最小汉明距离d是线性分组码的重要参数乙(n,ķ,d). 因此,对于给定的组合,了解理论上是否存在线性分组码是很有用的。R和d. 特别是,对于给定的最小汉明距离d我们将认为一个线性分组码优于另一个具有相同最小汉明距离的线性分组码d如果它有更高的码率R. 存在几个理论界限,我们将在下面简要讨论(Berlekamp,1984;Bossert,1999;Ling 和 Xing,2004;van Lint,1999)(另请参见图 2.22)。满足理论上相等界限的分组码称为最优码。
单例界
最简单的界就是所谓的单例界。对于线性块码乙(n,ķ,d)它是由
ķ≤n−d+1.
一个线性块代码,它满足具有相等性的 Singleton 约束,根据ķ=n−d+1称为MDS(最大可分离距离)。MDS 码的重要代表是 Reed-Solomon 码,例如,在音频光盘中的通道编码方案中使用(另见第 2.3.7 节)。
Sphere Packing Bound
所谓的 sphere Packing bound 或 Hamming bound 可以推导出一个线性的和心电图 = ⌊(d−1)/2⌋-纠错q-nary 块代码乙(n,ķ,d)通过考虑代码空间内的修正球Fqn. 每个修正球总共包含
∑一世=0和C这r(n 一世)(q−1)一世
代码空间中的向量Fqn. 由于每个码字都有一个修正球,我们有米=qķ修正球。任何半径修正球内的向量总数和心电图 然后由
qķ∑一世=0和心电图 (n 一世)(q−1)一世
因为这个数必须小于等于最大数|Fqn|=qn有限向量空间中的向量Fqn, 球体包装界
qķ∑一世=0和心电图(n 一世)(q−1)一世≤qn
数学代写|编码理论作业代写Coding Theory代考|Plotkin’s (u|v) Code Construction
与上述代码结构相比,Plotkin 最初提出的 (u|v) 代码结构采用两个线性块代码乙(n1,ķ1,d1)和乙(n2,ķ2,d2)带码字长n1和n2, 信息字长ķ1和ķ2和最小汉明距离d1和d2. 为了简化,我们用适当数量的零填充具有较小码字长度的块码的码字。此步骤称为零填充。让在和在是从线性块码中获得的两个任意码字乙(n1,ķ1,d1)和乙(n2,ķ2,d2)分别。12然后我们有
在={(b1∣0,…,0),n1<n2 b1,n1≥n2
和
在={b2,n1<n2 (b2∣0,…,0),n1≥n2
用任意选择的代码字b1∈乙(n1,ķ1,d1)和b2∈乙(n2,ķ2,d2). 我们现在识别代码字在和在与原始代码乙(n1,ķ1,d1)和乙(n2,ķ2,d2),即我们写在∈乙(n1,ķ1,d1)和在∈乙(n2,ķ2,d2). 然后由 Plotkin 的 (u|v) 代码构造产生的代码由下式给出
\mathbb{B}^{\prime}\left(n^{\prime}, k^{\prime}, d^{\prime}\right)=\left{(\mathbf{u} \mid \mathbf {u}+\mathbf{v}): \mathbf{u} \in \mathbb{B}\left(n_{1}, k_{1}, d_{1}\right) \wedge \mathbf{v} \in \mathbb{B}\left(n_{2}, k_{2}, d_{2}\right)\right}\mathbb{B}^{\prime}\left(n^{\prime}, k^{\prime}, d^{\prime}\right)=\left{(\mathbf{u} \mid \mathbf {u}+\mathbf{v}): \mathbf{u} \in \mathbb{B}\left(n_{1}, k_{1}, d_{1}\right) \wedge \mathbf{v} \in \mathbb{B}\left(n_{2}, k_{2}, d_{2}\right)\right}
此代码构造创建形式的所有向量(在∣在+在)通过连接所有可能的向量在和在+在和在∈乙(n1,ķ1,d1)和在∈乙(n2,ķ2,d2). 生成的代码具有以下代码参数的特征
\begin{对齐} &n^{\prime}=2 \max \left{n_{1}, n_{2}\right} \ &k^{\prime}=k_{1}+k_{2}, \ &d ^{\prime}=\min \left{2 d_{1}, d_{2}\right} \end{aligned}\begin{对齐} &n^{\prime}=2 \max \left{n_{1}, n_{2}\right} \ &k^{\prime}=k_{1}+k_{2}, \ &d ^{\prime}=\min \left{2 d_{1}, d_{2}\right} \end{aligned}
数学代写|编码理论作业代写Coding Theory代考|Examples of Linear Block Codes
在本节中,我们将介绍一些重要的线性分组码。特别是,我们将考虑已经介绍的重复码、奇偶校验码和汉明码。此外,还讨论了单纯形码和 Reed-Muller 码及其关系(Berlekamp,1984;Bossert,1999;Lin 和 Costello,2004;Ling 和 Xing,2004)。
我们已经在章节中介绍了二进制三重重复代码1.3作为线性分组码的简单介绍性示例。在此特定代码中,二进制信息符号 0 或 1 分别与二进制代码字 000 或 111 一起传输。一般来说,字母表上的重复代码Fq分配给q-nary 信息符号在0这n- 维码字b=(在0,在0,…,在0). 很简单,这个块代码是线性的。最小汉明距离为
d=n.
因此,图中的重复码2.27是一个线性块码乙(n,1,n)能够检测到和这 =d−1=n−1错误或纠正和心电图 =⌊(d−1)/2⌋=⌊(n−1)/2⌋错误。码率是
R=1n.
为了纠错,最小距离解码可以通过多数解码方案来实现。解码器发出信息符号在^0最常出现在接收到的单词中。
重复代码的权重分布简单地由下式给出
在(X)=1+(q−1)Xn
虽然这种重复码的特点是码率低R,由于其简单性,它被用于一些通信标准中。例如,在短距离无线通信系统蓝牙吨米三重重复码被用作传输的基带数据包的数据包头的编码方案的一部分(蓝牙,2004)。
统计代写请认准statistics-lab™. statistics-lab™为您的留学生涯保驾护航。
金融工程代写
金融工程是使用数学技术来解决金融问题。金融工程使用计算机科学、统计学、经济学和应用数学领域的工具和知识来解决当前的金融问题,以及设计新的和创新的金融产品。
非参数统计代写
非参数统计指的是一种统计方法,其中不假设数据来自于由少数参数决定的规定模型;这种模型的例子包括正态分布模型和线性回归模型。
广义线性模型代考
广义线性模型(GLM)归属统计学领域,是一种应用灵活的线性回归模型。该模型允许因变量的偏差分布有除了正态分布之外的其它分布。
术语 广义线性模型(GLM)通常是指给定连续和/或分类预测因素的连续响应变量的常规线性回归模型。它包括多元线性回归,以及方差分析和方差分析(仅含固定效应)。
有限元方法代写
有限元方法(FEM)是一种流行的方法,用于数值解决工程和数学建模中出现的微分方程。典型的问题领域包括结构分析、传热、流体流动、质量运输和电磁势等传统领域。
有限元是一种通用的数值方法,用于解决两个或三个空间变量的偏微分方程(即一些边界值问题)。为了解决一个问题,有限元将一个大系统细分为更小、更简单的部分,称为有限元。这是通过在空间维度上的特定空间离散化来实现的,它是通过构建对象的网格来实现的:用于求解的数值域,它有有限数量的点。边界值问题的有限元方法表述最终导致一个代数方程组。该方法在域上对未知函数进行逼近。[1] 然后将模拟这些有限元的简单方程组合成一个更大的方程系统,以模拟整个问题。然后,有限元通过变化微积分使相关的误差函数最小化来逼近一个解决方案。
tatistics-lab作为专业的留学生服务机构,多年来已为美国、英国、加拿大、澳洲等留学热门地的学生提供专业的学术服务,包括但不限于Essay代写,Assignment代写,Dissertation代写,Report代写,小组作业代写,Proposal代写,Paper代写,Presentation代写,计算机作业代写,论文修改和润色,网课代做,exam代考等等。写作范围涵盖高中,本科,研究生等海外留学全阶段,辐射金融,经济学,会计学,审计学,管理学等全球99%专业科目。写作团队既有专业英语母语作者,也有海外名校硕博留学生,每位写作老师都拥有过硬的语言能力,专业的学科背景和学术写作经验。我们承诺100%原创,100%专业,100%准时,100%满意。
随机分析代写
随机微积分是数学的一个分支,对随机过程进行操作。它允许为随机过程的积分定义一个关于随机过程的一致的积分理论。这个领域是由日本数学家伊藤清在第二次世界大战期间创建并开始的。
时间序列分析代写
随机过程,是依赖于参数的一组随机变量的全体,参数通常是时间。 随机变量是随机现象的数量表现,其时间序列是一组按照时间发生先后顺序进行排列的数据点序列。通常一组时间序列的时间间隔为一恒定值(如1秒,5分钟,12小时,7天,1年),因此时间序列可以作为离散时间数据进行分析处理。研究时间序列数据的意义在于现实中,往往需要研究某个事物其随时间发展变化的规律。这就需要通过研究该事物过去发展的历史记录,以得到其自身发展的规律。
回归分析代写
多元回归分析渐进(Multiple Regression Analysis Asymptotics)属于计量经济学领域,主要是一种数学上的统计分析方法,可以分析复杂情况下各影响因素的数学关系,在自然科学、社会和经济学等多个领域内应用广泛。
MATLAB代写
MATLAB 是一种用于技术计算的高性能语言。它将计算、可视化和编程集成在一个易于使用的环境中,其中问题和解决方案以熟悉的数学符号表示。典型用途包括:数学和计算算法开发建模、仿真和原型制作数据分析、探索和可视化科学和工程图形应用程序开发,包括图形用户界面构建MATLAB 是一个交互式系统,其基本数据元素是一个不需要维度的数组。这使您可以解决许多技术计算问题,尤其是那些具有矩阵和向量公式的问题,而只需用 C 或 Fortran 等标量非交互式语言编写程序所需的时间的一小部分。MATLAB 名称代表矩阵实验室。MATLAB 最初的编写目的是提供对由 LINPACK 和 EISPACK 项目开发的矩阵软件的轻松访问,这两个项目共同代表了矩阵计算软件的最新技术。MATLAB 经过多年的发展,得到了许多用户的投入。在大学环境中,它是数学、工程和科学入门和高级课程的标准教学工具。在工业领域,MATLAB 是高效研究、开发和分析的首选工具。MATLAB 具有一系列称为工具箱的特定于应用程序的解决方案。对于大多数 MATLAB 用户来说非常重要,工具箱允许您学习和应用专业技术。工具箱是 MATLAB 函数(M 文件)的综合集合,可扩展 MATLAB 环境以解决特定类别的问题。可用工具箱的领域包括信号处理、控制系统、神经网络、模糊逻辑、小波、仿真等。
