如果你也在 怎样代写密码学Cryptography & Cryptanalysis这个学科遇到相关的难题,请随时右上角联系我们的24/7代写客服。
密码学创造了具有隐藏意义的信息;密码分析是破解这些加密信息以恢复其意义的科学。许多人用密码学一词来代替密码学;然而,重要的是要记住,密码学包括了密码学和密码分析。
statistics-lab™ 为您的留学生涯保驾护航 在代写密码学Cryptography & Cryptanalysis方面已经树立了自己的口碑, 保证靠谱, 高质且原创的统计Statistics代写服务。我们的专家在代写密码学Cryptography & Cryptanalysis代写方面经验极为丰富,各种代写密码学Cryptography & Cryptanalysis相关的作业也就用不着说。
我们提供的密码学Cryptography & Cryptanalysis及其相关学科的代写,服务范围广, 其中包括但不限于:
- Statistical Inference 统计推断
- Statistical Computing 统计计算
- Advanced Probability Theory 高等概率论
- Advanced Mathematical Statistics 高等数理统计学
- (Generalized) Linear Models 广义线性模型
- Statistical Machine Learning 统计机器学习
- Longitudinal Data Analysis 纵向数据分析
- Foundations of Data Science 数据科学基础
数学代写|密码学作业代写Cryptography & Cryptanalysis代考|Remark and Introduction to Chapters
In this book, we focus on VC algorithms satisfying strong security and no pixel expansion. The secret image is a grayscale image, whereas the shares are meaningless. Under these conditions, we review important efforts in improving the visual quality of the reconstructed secret image.
This book consists of seven chapters and the topics are arranged as follows.
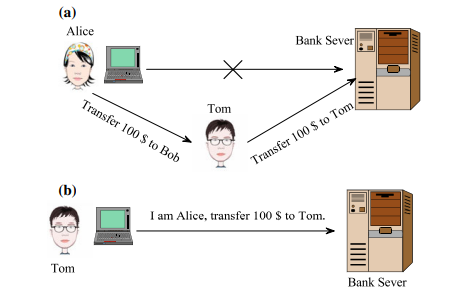
In Chap. 2, after introducing the basic framework of visual cryptography, we review the three basic VC schemes, the classic deterministic VC, the probabilistic $\mathrm{VC}$ and the random grid VC. The security issue including the weak security and replacement attacks will also be briefly reviewed.
In Chap. 3, we introduce the problem of digital halftoning and important halftoning schemes, including simple bi-level quantization, ordered dithering, error diffusion and direct binary search. The quality measures for halftone image are also reviewed. Furthermore, we introduce the residual variance measure that will be used to evaluate the quality of recovered secret image in VC. The purpose of this chapter is to introduce to the reader a self-contained background for digital halftoning. For the VC algorithms we are focusing to, the secret images and/or cover images are grayscale images.
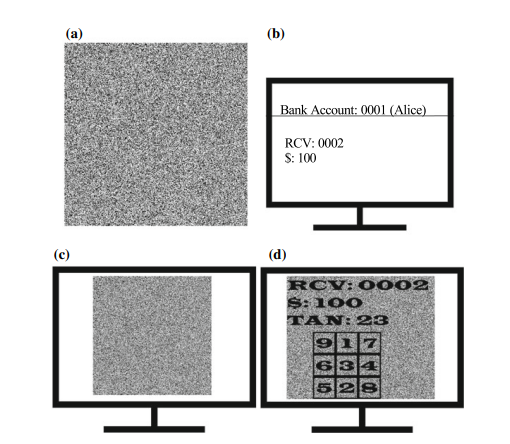
In Chap. 4, we introduce important algorithms in improving visual quality for the share images in extended VC, i.e., VC with meaningful shares. For binary cover image, we introduce three important algorithms, the basic extended VC, user-friendly random grid, and pixel swapping algorithm. For halftone shares, we introduce error diffusion based algorithms, and an improvement of this algorithm by including a hidden watermark, for authentication purpose.
In Chap. 5, we introduce the VC problem for grayscale secret image. Then the efforts in improving size-invariant VC are reviewed. For probabilistic VC, Wang’s size-invariant algorithm and our analysis-by-synthesis algorithms will be introduced. For random grid VC, we introduce the blue noise approach and our analysis-bysynthesis approach.
In Chap. 6, the vector VC approach will be comprehensively reviewed. For halftone secret image, we introduce Hou’s block encoding algorithm, Lee’s block
encoding algorithm, and our local blackness preserving algorithm. From Lee’s work, we formally define the vector VC scheme, which is then improved by a vector VC in the analysis-by-synthesis framework.
The Chap. 7 concludes this book with a short summary and discussion of future works.
数学代写|密码学作业代写Cryptography & Cryptanalysis代考|Framework of Visual Secret Sharing
In a $(k, n)$-threshold visual cryptography (visual secret sharing) problem [13], a secret image $\mathbf{s}$ is shared between $n$ parties, called participants. Each participant obtains one share image. If less than $k$ shares are obtained, it is not possible to infer s from them. But. if $k$ or more than $k$ shares are obtained. then the secret $s$ can be revealed by stacking these shares, producing different average brightnesses for the white secret pixels and black secret pixels. For visual cryptography, the shares are usually printed on transparencies, and decoding corresponds to stacking the shares. The stacking result is called the target image.
The above threshold schemes can be extended to more general access structure [1]. There are two sets of participants, the forbidden set $\Gamma_{\text {Forb }}$, and the qualified set $\Gamma_{\text {Qual }}$. For a group of participants $P$, if $P \in \Gamma_{\text {Forb }}$, then it should be impossible to infer $s$ from the shares owned by these participants. If $P \in \Gamma_{\text {Qual }}$, then by stacking all the shares owned by these participants, the content of the secret should be recovered with sufficient contrast.
For example, for a $(3,3)$-threshold scheme, we have
$$
\begin{aligned}
&\Gamma_{\text {Qual }}={{1,2,3}}, \
&\Gamma_{\text {Forb }}={{1},{2},{3},{1,2},{1,3},{2,3}}
\end{aligned}
$$
数学代写|密码学作业代写Cryptography & Cryptanalysis代考|A Note on Color Convention
For monochrome, there are two conventional ways of numerical representation of colors. For the first approach, the axis is lightness, where larger value corresponds to brighter color. Such a convention is widely used in digital image processing and digital display. For the second approach, the axis represents the amount of absorption
of light, where larger value corresponds to darker color. Such a convention is adopted in printing, visual cryptography and QR (Quick Response) code.
Visual cryptography, in its strict sense, needs to print its shares on transparencies. So, larger value should correspond to higher darkness. In this book, we adopt this convention. If an image is normalized to the range $[0,1]$, then ‘ 0 ‘ corresponds to the brightest color (White) and ‘ 1 ‘ (for normalized image) or ‘ $255^{\text {‘ }}$ (for 8 -bit representation) corresponds to the darkest color (Black). In summary, we use the following numerical representation of pixels:
$$
\begin{aligned}
&\square \leftrightarrow 1, \
&\square \leftrightarrow 0 .
\end{aligned}
$$Deterministic VC is the type of VC proposed by Naor and Shamir [13]. The prefix ‘deterministic’ is used here to distinguish it from the probabilistic schemes. Please note that deterministic doesn’t mean that every step of the algorithm is deterministic. For deterministic VC, each secret pixel is represented by a block on share images. Usually, the shape of the block is a square, in order to preserve the aspect ratio of objects in the secret image onto the target image.
密码学代写
数学代写|密码学作业代写Cryptography & Cryptanalysis代考|Remark and Introduction to Chapters
在本书中,我们关注的是满足强安全性和无像素扩展的 VC 算法。秘密图像是灰度图像,而共享是无意义的。在这些条件下,我们回顾了在提高重建秘密图像的视觉质量方面所做的重要努力。
本书共七章,主题安排如下。
在第一章。2、介绍了视觉密码学的基本框架后,我们回顾了三种基本的VC方案,经典的确定性VC,概率性的在C和随机网格 VC。还将简要回顾包括弱安全和替换攻击在内的安全问题。
在第一章。3、我们介绍了数字半色调问题和重要的半色调方案,包括简单的双层量化、有序抖动、误差扩散和直接二分搜索。还回顾了半色调图像的质量测量。此外,我们引入了残差方差度量,用于评估 VC 中恢复的秘密图像的质量。本章的目的是向读者介绍一个独立的数字半色调背景。对于我们关注的 VC 算法,秘密图像和/或封面图像是灰度图像。
在第一章。4,我们介绍了提高扩展VC中共享图像视觉质量的重要算法,即具有有意义共享的VC。对于二值封面图像,我们介绍了三种重要的算法,基本的扩展VC、用户友好的随机网格和像素交换算法。对于半色调共享,我们引入了基于误差扩散的算法,并通过包含隐藏水印对该算法进行了改进,以用于身份验证。
在第一章。5、我们介绍了灰度秘密图像的VC问题。然后回顾了改进大小不变VC的努力。对于概率 VC,将介绍 Wang 的大小不变算法和我们的综合分析算法。对于随机网格 VC,我们介绍了蓝噪声方法和我们的综合分析方法。
在第一章。6、对矢量VC方式进行全面回顾。对于半色调秘密图像,我们介绍侯氏块编码算法,李氏块
编码算法,以及我们的局部黑度保持算法。从 Lee 的工作中,我们正式定义了向量 VC 方案,然后在综合分析框架中通过向量 VC 对其进行了改进。
章。7 以对未来工作的简短总结和讨论结束本书。
数学代写|密码学作业代写Cryptography & Cryptanalysis代考|Framework of Visual Secret Sharing
在一个(ķ,n)- 阈值视觉密码学(视觉秘密共享)问题[13],一个秘密图像s之间共享n各方,称为参与者。每个参与者获得一个共享图像。如果小于ķ获得股份后,无法从中推断出 s。但。如果ķ或超过ķ获得股份。然后是秘密s可以通过堆叠这些份额来显示,为白色秘密像素和黑色秘密像素产生不同的平均亮度。对于视觉密码学,共享通常打印在透明胶片上,解码对应于堆叠共享。堆叠结果称为目标图像。
上述阈值方案可以扩展到更一般的访问结构[1]。有两组参与者,禁止组Γ福布 , 和合格集Γ哪一个 . 对于一组参与者磷, 如果磷∈Γ福布 ,那么应该无法推断s来自这些参与者拥有的股份。如果磷∈Γ哪一个 ,那么通过堆叠这些参与者所拥有的所有股份,应该以足够的对比度恢复秘密的内容。
例如,对于一个(3,3)-阈值方案,我们有
Γ哪一个 =1,2,3, Γ福布 =1,2,3,1,2,1,3,2,3
数学代写|密码学作业代写Cryptography & Cryptanalysis代考|A Note on Color Convention
对于单色,有两种传统的颜色数字表示方式。对于第一种方法,轴是亮度,其中较大的值对应于较亮的颜色。这种约定广泛用于数字图像处理和数字显示。对于第二种方法,轴表示吸收量
光,其中较大的值对应于较暗的颜色。打印、视觉密码学和 QR(快速响应)代码都采用了这样的约定。
严格意义上的视觉密码学需要将其份额打印在透明胶片上。因此,较大的值应对应于较高的暗度。在本书中,我们采用了这个约定。如果图像被归一化到范围[0,1],那么’0’对应最亮的颜色(白色)和’1’(用于标准化图像)或’255‘ (对于 8 位表示)对应于最深的颜色(黑色)。总之,我们使用以下像素的数字表示:
↔1, ↔0.确定性 VC 是 Naor 和 Shamir [13] 提出的 VC 类型。此处使用前缀“确定性”将其与概率方案区分开来。请注意,确定性并不意味着算法的每一步都是确定性的。对于确定性 VC,每个秘密像素都由共享图像上的一个块表示。通常,块的形状是正方形,以保持秘密图像中对象在目标图像上的纵横比。
统计代写请认准statistics-lab™. statistics-lab™为您的留学生涯保驾护航。
金融工程代写
金融工程是使用数学技术来解决金融问题。金融工程使用计算机科学、统计学、经济学和应用数学领域的工具和知识来解决当前的金融问题,以及设计新的和创新的金融产品。
非参数统计代写
非参数统计指的是一种统计方法,其中不假设数据来自于由少数参数决定的规定模型;这种模型的例子包括正态分布模型和线性回归模型。
广义线性模型代考
广义线性模型(GLM)归属统计学领域,是一种应用灵活的线性回归模型。该模型允许因变量的偏差分布有除了正态分布之外的其它分布。
术语 广义线性模型(GLM)通常是指给定连续和/或分类预测因素的连续响应变量的常规线性回归模型。它包括多元线性回归,以及方差分析和方差分析(仅含固定效应)。
有限元方法代写
有限元方法(FEM)是一种流行的方法,用于数值解决工程和数学建模中出现的微分方程。典型的问题领域包括结构分析、传热、流体流动、质量运输和电磁势等传统领域。
有限元是一种通用的数值方法,用于解决两个或三个空间变量的偏微分方程(即一些边界值问题)。为了解决一个问题,有限元将一个大系统细分为更小、更简单的部分,称为有限元。这是通过在空间维度上的特定空间离散化来实现的,它是通过构建对象的网格来实现的:用于求解的数值域,它有有限数量的点。边界值问题的有限元方法表述最终导致一个代数方程组。该方法在域上对未知函数进行逼近。[1] 然后将模拟这些有限元的简单方程组合成一个更大的方程系统,以模拟整个问题。然后,有限元通过变化微积分使相关的误差函数最小化来逼近一个解决方案。
tatistics-lab作为专业的留学生服务机构,多年来已为美国、英国、加拿大、澳洲等留学热门地的学生提供专业的学术服务,包括但不限于Essay代写,Assignment代写,Dissertation代写,Report代写,小组作业代写,Proposal代写,Paper代写,Presentation代写,计算机作业代写,论文修改和润色,网课代做,exam代考等等。写作范围涵盖高中,本科,研究生等海外留学全阶段,辐射金融,经济学,会计学,审计学,管理学等全球99%专业科目。写作团队既有专业英语母语作者,也有海外名校硕博留学生,每位写作老师都拥有过硬的语言能力,专业的学科背景和学术写作经验。我们承诺100%原创,100%专业,100%准时,100%满意。
随机分析代写
随机微积分是数学的一个分支,对随机过程进行操作。它允许为随机过程的积分定义一个关于随机过程的一致的积分理论。这个领域是由日本数学家伊藤清在第二次世界大战期间创建并开始的。
时间序列分析代写
随机过程,是依赖于参数的一组随机变量的全体,参数通常是时间。 随机变量是随机现象的数量表现,其时间序列是一组按照时间发生先后顺序进行排列的数据点序列。通常一组时间序列的时间间隔为一恒定值(如1秒,5分钟,12小时,7天,1年),因此时间序列可以作为离散时间数据进行分析处理。研究时间序列数据的意义在于现实中,往往需要研究某个事物其随时间发展变化的规律。这就需要通过研究该事物过去发展的历史记录,以得到其自身发展的规律。
回归分析代写
多元回归分析渐进(Multiple Regression Analysis Asymptotics)属于计量经济学领域,主要是一种数学上的统计分析方法,可以分析复杂情况下各影响因素的数学关系,在自然科学、社会和经济学等多个领域内应用广泛。
MATLAB代写
MATLAB 是一种用于技术计算的高性能语言。它将计算、可视化和编程集成在一个易于使用的环境中,其中问题和解决方案以熟悉的数学符号表示。典型用途包括:数学和计算算法开发建模、仿真和原型制作数据分析、探索和可视化科学和工程图形应用程序开发,包括图形用户界面构建MATLAB 是一个交互式系统,其基本数据元素是一个不需要维度的数组。这使您可以解决许多技术计算问题,尤其是那些具有矩阵和向量公式的问题,而只需用 C 或 Fortran 等标量非交互式语言编写程序所需的时间的一小部分。MATLAB 名称代表矩阵实验室。MATLAB 最初的编写目的是提供对由 LINPACK 和 EISPACK 项目开发的矩阵软件的轻松访问,这两个项目共同代表了矩阵计算软件的最新技术。MATLAB 经过多年的发展,得到了许多用户的投入。在大学环境中,它是数学、工程和科学入门和高级课程的标准教学工具。在工业领域,MATLAB 是高效研究、开发和分析的首选工具。MATLAB 具有一系列称为工具箱的特定于应用程序的解决方案。对于大多数 MATLAB 用户来说非常重要,工具箱允许您学习和应用专业技术。工具箱是 MATLAB 函数(M 文件)的综合集合,可扩展 MATLAB 环境以解决特定类别的问题。可用工具箱的领域包括信号处理、控制系统、神经网络、模糊逻辑、小波、仿真等。
