计算机代写|计算机视觉代写Computer Vision代考|CS231
如果你也在 怎样代写计算机视觉Computer Vision这个学科遇到相关的难题,请随时右上角联系我们的24/7代写客服。
计算机视觉是人工智能(AI)的一个领域,使计算机和系统能够从数字图像、视频和其他视觉输入中获得有意义的信息–并根据这些信息采取行动或提出建议。
statistics-lab™ 为您的留学生涯保驾护航 在代写计算机视觉Computer Vision方面已经树立了自己的口碑, 保证靠谱, 高质且原创的统计Statistics代写服务。我们的专家在代写计算机视觉Computer Vision方面经验极为丰富,各种代写计算机视觉Computer Vision相关的作业也就用不着说。
我们提供的计算机视觉Computer Vision及其相关学科的代写,服务范围广, 其中包括但不限于:
- Statistical Inference 统计推断
- Statistical Computing 统计计算
- Advanced Probability Theory 高等楖率论
- Advanced Mathematical Statistics 高等数理统计学
- (Generalized) Linear Models 广义线性模型
- Statistical Machine Learning 统计机器学习
- Longitudinal Data Analysis 纵向数据分析
- Foundations of Data Science 数据科学基础
计算机代写|计算机视觉代写Computer Vision代考|Detection of Translation
Suppose that the position of the pixel at time $t_k$ is $(x, y)$ and the position of the pixel at time $t_{k+1}$ moves to $(x+\mathrm{d} x, y+\mathrm{d} y)$. It is generally assumed that the gray level of the pixel itself remains unchanged during this period of time; then
$$
f\left(x+\mathrm{d} x, y+\mathrm{d} y, t_{k+1}\right)=f\left(x, y, t_k\right)
$$
According to the properties of Fourier transform, there are
$$
\begin{gathered}
F_k(u, v)=f\left(x, y, t_k\right) \
F_{k+1}(u, v)=f\left(x+\mathrm{d} x, y+\mathrm{d} y, t_{k+1}\right)
\end{gathered}
$$
It can be obtained with the help of translation properties:
$$
F_{k+1}(u, v)=F_k(u, v) \exp [j 2 \pi(u \mathrm{~d} x+v \mathrm{~d} y)]
$$
Equation (4.24) shows that the phase angle difference of the Fourier transform of the two images taken at time $t_k$ and time $t_{k+1}$ is
$$
\mathrm{d} \theta(u, v)=2 \pi(u \mathrm{~d} x, v \mathrm{~d} y)
$$
Taking into account the separability of Fourier transform, it can be obtained from Eq. (4.25):
$$
\begin{aligned}
& \mathrm{d} x=\frac{d \theta_x(u)}{2 \pi u} \
& \mathrm{~d} y=\frac{d \theta_y(v)}{2 \pi v}
\end{aligned}
$$
In Eq. (4.26) and (4.27), $\mathrm{d} \theta_x(u)$ and $\mathrm{d} \theta_y(v)$ are the difference between the phase angle of the Fourier transform projected on the $X$ axis and the $Y$ axis by $f\left(x, y, t_k\right)$ and $f\left(x, y, t_k+1\right)$, respectively. Due to the non-uniqueness of the phase angle, the following methods can be used when calculating $\mathrm{d} \theta_x(u)$ and $\mathrm{d} \theta_y(v)$. Suppose the variation range of $\mathrm{d} x$ satisfies
$$
\left|\frac{\mathrm{d} x}{L_x}\right|<\frac{1}{2 K}
$$
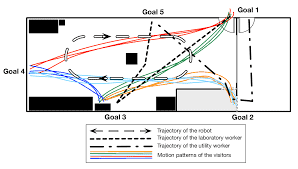
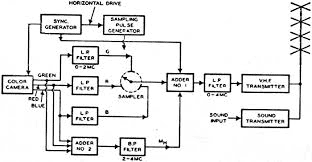
计算机代写|计算机视觉代写Computer Vision代考|Detection of Movement Direction
In many applications, certain specific motion patterns need to be determined. In this case, image-based information and motion-based information can be combined. Motion information can be obtained by determining a specific difference between images that are acquired sequentially. Generally, in order to improve the accuracy and use the spatial distribution information, the image is often divided into blocks, and then two moving image blocks with a time difference (one collected at time $t$ and one collected at time $t+\mathrm{d} t$ ) are considered. The direction of motion can use the following four kinds of calculation for difference image:
$$
\begin{aligned}
& U=\left|f_t-f_{t+\mathrm{d} t t}\right| \
& D=\left|f_t-f_{t+\mathrm{d} t \mid}\right| \
& L=\left|f_t-f_{t+\mathrm{d} t \leftarrow}\right| \
& R=\left|f_t-f_{t+\mathrm{d} t \rightarrow}\right|
\end{aligned}
$$
where the arrow represents the direction of image motion, such as $\downarrow$ represents the image frame $I_{t+\mathrm{d} t}$ moves downward relative to the previous frame $I_t$.
The amplitude of motion can be obtained by summing the area of the image block. This sum can be quickly calculated with the help of the integral image below.
Integral image is a matrix representation method that maintains the global information of the image. In the integral image, the value $I(x, y)$ at the position $(x, y)$ represents the sum of all the pixel values at the upper left of the position in the original image $f(x, y)$ :
$$
f(x, y)=\sum_{p \leq x, q \leq y} f(p, q)
$$
The construction of the integral image can be carried out by scanning the image only once by means of a loop:
- Let $s(x, y)$ represent the cumulative sum of a row of pixels, $s(x,-1)=0$.
- Let $I(x, y)$ be an integral image, $I(-1, y)=0$.
计算机视觉代考
计算机代写|计算机视觉代写Computer Vision代考|Detection of Translation
假设像素点在时间的位置 $t_k$ 是 $(x, y)$ 和像素在时间的位置 $t_{k+1}$ 移动到 $(x+\mathrm{d} x, y+\mathrm{d} y)$. 一般假设像素 本身的灰度值在这段时间内保持不变; 然后
$$
f\left(x+\mathrm{d} x, y+\mathrm{d} y, t_{k+1}\right)=f\left(x, y, t_k\right)
$$
根据傅里叶变换的性质,有
$$
F_k(u, v)=f\left(x, y, t_k\right) F_{k+1}(u, v)=f\left(x+\mathrm{d} x, y+\mathrm{d} y, t_{k+1}\right)
$$
它可以借助翻译属性获得:
$$
F_{k+1}(u, v)=F_k(u, v) \exp [j 2 \pi(u \mathrm{~d} x+v \mathrm{~d} y)]
$$
式 (4.24) 表明,时刻拍摄的两幅图像的傅里叶变换相位角差 $t_k$ 和时间 $t_{k+1}$ 是
$$
\mathrm{d} \theta(u, v)=2 \pi(u \mathrm{~d} x, v \mathrm{~d} y)
$$
考虑到傅立叶变换的可分离性,可由式 (1) 得到。(4.25):
$$
\mathrm{d} x=\frac{d \theta_x(u)}{2 \pi u} \quad \mathrm{~d} y=\frac{d \theta_y(v)}{2 \pi v}
$$
在等式中。(4.26) 和 (4.27), $\mathrm{d} \theta_x(u)$ 和 $\mathrm{d} \theta_y(v)$ 是投射在 $X$ 轴和 $Y$ 轴心 $f\left(x, y, t_k\right)$ 和 $f\left(x, y, t_k+1\right)$ , 分别。由于相位角的非唯一性,计算时可采用以下方法 $\mathrm{d} \theta_x(u)$ 和 $\mathrm{d} \theta_y(v)$. 假设变化范围为 $\mathrm{d} x$ 满足
$$
\left|\frac{\mathrm{d} x}{L_x}\right|<\frac{1}{2 K}
$$
计算机代写|计算机视觉代写Computer Vision代考|Detection of Movement Direction
在许多应用中,需要确定某些特定的运动模式。在这种情况下,可以组合基于图像的信息和基于运动的信 息。可以通过确定顺序获取的图像之间的特定差异来获得运动信息。通常,为了提高精度和利用空间分布 信息,往往将图像分成块,然后将两个具有时间差的运动图像块(一个在时间上采集 $t$ 和一个在时间收集 $t+\mathrm{d} t)$ 被考虑。运动方向可以用以下四种差分图像计算:
$$
U=\left|f_t-f_{t+\mathrm{d} t t}\right| \quad D=\left|f_t-f_{t+\mathrm{d} t \mid}\right| L=\left|f_t-f_{t+\mathrm{d} t \leftarrow}\right| \quad R=\left|f_t-f_{t+\mathrm{d} t \rightarrow}\right|
$$
其中箭头代表图像运动的方向,如】表示图像帧 $I_{t+\mathrm{d} t}$ 相对于前一帧向下移动 $I_t$.
可以通过对图像块的面积求和来获得运动幅度。可以借助下面的积分图像快速计算出这个总和。 积分图像是一种保持图像全局信息的矩阵表示方法。在积分图像中,值 $I(x, y)$ 在那个位置 $(x, y)$ 表示原 图像中该位置左上角所有像素值的总和 $f(x, y)$ :
$$
f(x, y)=\sum_{p \leq x, q \leq y} f(p, q)
$$
积分图像的构造可以通过循环仅扫描一次图像来进行:
- 让 $s(x, y)$ 表示一行像素的侽加和, $s(x,-1)=0$.
- 让 $I(x, y)$ 成为一个完整的形象, $I(-1, y)=0$.
统计代写请认准statistics-lab™. statistics-lab™为您的留学生涯保驾护航。统计代写|python代写代考
随机过程代考
在概率论概念中,随机过程是随机变量的集合。 若一随机系统的样本点是随机函数,则称此函数为样本函数,这一随机系统全部样本函数的集合是一个随机过程。 实际应用中,样本函数的一般定义在时间域或者空间域。 随机过程的实例如股票和汇率的波动、语音信号、视频信号、体温的变化,随机运动如布朗运动、随机徘徊等等。
贝叶斯方法代考
贝叶斯统计概念及数据分析表示使用概率陈述回答有关未知参数的研究问题以及统计范式。后验分布包括关于参数的先验分布,和基于观测数据提供关于参数的信息似然模型。根据选择的先验分布和似然模型,后验分布可以解析或近似,例如,马尔科夫链蒙特卡罗 (MCMC) 方法之一。贝叶斯统计概念及数据分析使用后验分布来形成模型参数的各种摘要,包括点估计,如后验平均值、中位数、百分位数和称为可信区间的区间估计。此外,所有关于模型参数的统计检验都可以表示为基于估计后验分布的概率报表。
广义线性模型代考
广义线性模型(GLM)归属统计学领域,是一种应用灵活的线性回归模型。该模型允许因变量的偏差分布有除了正态分布之外的其它分布。
statistics-lab作为专业的留学生服务机构,多年来已为美国、英国、加拿大、澳洲等留学热门地的学生提供专业的学术服务,包括但不限于Essay代写,Assignment代写,Dissertation代写,Report代写,小组作业代写,Proposal代写,Paper代写,Presentation代写,计算机作业代写,论文修改和润色,网课代做,exam代考等等。写作范围涵盖高中,本科,研究生等海外留学全阶段,辐射金融,经济学,会计学,审计学,管理学等全球99%专业科目。写作团队既有专业英语母语作者,也有海外名校硕博留学生,每位写作老师都拥有过硬的语言能力,专业的学科背景和学术写作经验。我们承诺100%原创,100%专业,100%准时,100%满意。
机器学习代写
随着AI的大潮到来,Machine Learning逐渐成为一个新的学习热点。同时与传统CS相比,Machine Learning在其他领域也有着广泛的应用,因此这门学科成为不仅折磨CS专业同学的“小恶魔”,也是折磨生物、化学、统计等其他学科留学生的“大魔王”。学习Machine learning的一大绊脚石在于使用语言众多,跨学科范围广,所以学习起来尤其困难。但是不管你在学习Machine Learning时遇到任何难题,StudyGate专业导师团队都能为你轻松解决。
多元统计分析代考
基础数据: $N$ 个样本, $P$ 个变量数的单样本,组成的横列的数据表
变量定性: 分类和顺序;变量定量:数值
数学公式的角度分为: 因变量与自变量
时间序列分析代写
随机过程,是依赖于参数的一组随机变量的全体,参数通常是时间。 随机变量是随机现象的数量表现,其时间序列是一组按照时间发生先后顺序进行排列的数据点序列。通常一组时间序列的时间间隔为一恒定值(如1秒,5分钟,12小时,7天,1年),因此时间序列可以作为离散时间数据进行分析处理。研究时间序列数据的意义在于现实中,往往需要研究某个事物其随时间发展变化的规律。这就需要通过研究该事物过去发展的历史记录,以得到其自身发展的规律。
回归分析代写
多元回归分析渐进(Multiple Regression Analysis Asymptotics)属于计量经济学领域,主要是一种数学上的统计分析方法,可以分析复杂情况下各影响因素的数学关系,在自然科学、社会和经济学等多个领域内应用广泛。
MATLAB代写
MATLAB 是一种用于技术计算的高性能语言。它将计算、可视化和编程集成在一个易于使用的环境中,其中问题和解决方案以熟悉的数学符号表示。典型用途包括:数学和计算算法开发建模、仿真和原型制作数据分析、探索和可视化科学和工程图形应用程序开发,包括图形用户界面构建MATLAB 是一个交互式系统,其基本数据元素是一个不需要维度的数组。这使您可以解决许多技术计算问题,尤其是那些具有矩阵和向量公式的问题,而只需用 C 或 Fortran 等标量非交互式语言编写程序所需的时间的一小部分。MATLAB 名称代表矩阵实验室。MATLAB 最初的编写目的是提供对由 LINPACK 和 EISPACK 项目开发的矩阵软件的轻松访问,这两个项目共同代表了矩阵计算软件的最新技术。MATLAB 经过多年的发展,得到了许多用户的投入。在大学环境中,它是数学、工程和科学入门和高级课程的标准教学工具。在工业领域,MATLAB 是高效研究、开发和分析的首选工具。MATLAB 具有一系列称为工具箱的特定于应用程序的解决方案。对于大多数 MATLAB 用户来说非常重要,工具箱允许您学习和应用专业技术。工具箱是 MATLAB 函数(M 文件)的综合集合,可扩展 MATLAB 环境以解决特定类别的问题。可用工具箱的领域包括信号处理、控制系统、神经网络、模糊逻辑、小波、仿真等。